What is a DDoS Attack? The Complete Guide
August 01, 2022 • security

A Distributed Denial of Service (DDoS) attack is a malicious attempt to make an online service unavailable by overwhelming it with traffic from multiple sources. This guide will teach you everything you need to know about DDoS attacks, including how to defend against them.
What is a DDoS Attack?
A DDoS attack is an illegal variety of hacking in which a flood of traffic is directed to a server to prevent people from accessing linked online services and sites.
There are many reasons why people might want to launch a DDoS attack. Some people might be angry customers or hacktivists who want to bring down a company’s servers just to make a statement. Others might do it for fun or in protest of something.
Although DDoS attacks may be used to steal from a company, they are primarily a financial worry. For example, one firm’s internet activities are disrupted or halted by a rival to steal clients. Another example is extortion, in which attackers target a firm and install hostware or ransomware on their servers before demanding that they pay a huge ransom to undo the damage.
Unfortunately, DDoS assaults have become more frequent and more potent in recent years as the internet has become increasingly essential to businesses and individuals. The rise in IoT devices has also played a role in this, as many of these devices are easy to hack and can be used to create botnets that launch attacks.
How does a DDoS attack work?
A DDoS attack is when many hacked computers are used to send traffic to a website or server, making it difficult for the site or server to function. This can be done by remotely controlling these computers using a botnet, which is a collection of bots.
After an established botnet, the attacker may send remote commands to each bot to direct an assault. This can overload the target’s IP address with requests, resulting in a denial-of-service attack on routine traffic.
Because each bot is an actual device on the internet, it can be challenging to determine if abnormal traffic is expected.
How to identify a DDoS attack
The trickiest thing about a DDoS attack is that you can’t see any warning signs. Usually, prominent hacking collectives will give warnings before they launch an attack, but most attackers will just order an assault without notice.
People may not always tell you if they do not like the content on your website. They might be afraid to say anything. But if something is wrong, they will tell you. They might not tell you at first, but they will later. That’s because people usually don’t check your website as you do. You think everything is okay, but sometimes it is not. You need to be careful because sometimes there are problems that you cannot see at first.
Finding the source of a Distributed Denial of Service attack can be difficult. The attack can go on for many hours, and you may be unable to stop it immediately. This means that you will lose revenue and service for hours.
Mitigate a DDoS attack
The best way to protect your website from a DDoS attack is to detect it as soon as possible. If you notice any of the following signs, it means that you are currently under a DDoS attack:
- Slow loading
- The server responds with a 503
- The TTL times out
- An excessive amount of spam comments
- Network suddenly disconnected
- There are typical patterns in traffic, like spikes at odd hours
The most common types of DDoS attacks
DDoS attacks are used by criminals to target a variety of network connections. Understanding the basics of networking is essential to understanding how several types of DDoS attacks work.
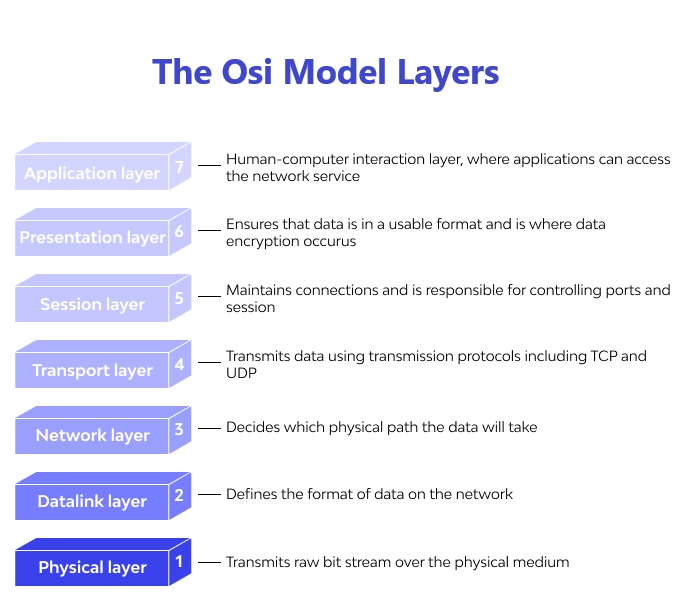
An Internet connection has several distinct parts, also known as layers. Each layer has a specific purpose.
The OSI model is a graphical way of representing how various parts of a network are connected. However, the current Internet is based on a more straightforward system called TCP/IP. The OSI model is still in use because it helps people see and understand how networks work and troubleshoot any possible problems.
There are three types of DDoS attacks. The first type is when a device is overloaded with traffic. The second type is when a network is overloaded with traffic. The third type happens when an attacker uses more than one attack vector to overwhelm their target.
Application layer attacks
The user experience begins when a person first contacts the internet. Application layer DDoS attacks stop software from working so people can’t see any content. Web servers are often targeted in these attacks, but other programs such as SIP voice services and BGP can also be attacked.
The TCP/IP protocol can transfer data between devices on a network. But this protocol is highly vulnerable to DDoS attacks. This means someone can attack your device and stop it from working by sending a lot of data simultaneously. Even though some people may be frustrated by this, using a secure protocol for online transactions is still essential. Using encryption for communication protects both parties from interception and eavesdropping. Most DDoS attacks use far fewer packets per second.
This attack would require using the specific protocol of the targeted application, which can involve handshakes and compliance. These kinds of assaults will be driven primarily by IoT gadgets that can’t easily be spoofed.
Example of application DDoS attacks
HTTP flood
This is a server that accepts requests from a lot of different computers. This method, like refreshing a web page on many PCs simultaneously, sends many HTTP requests to the server, overloading it. The attack may be simple or complex.
One URL can be accessed using the same range of attacking IP addresses, referring sites, and user agents. This makes it easier for the attacker to find and use the target URL. More complex variations may target a variety of URLs using various referrers and user agents to access them.
Protocol attacks
A Protocol Flood is a DDoS attack that sends lots of traffic to a service or network, making it hard to use. Exploiting vulnerabilities in the layer three and layer four protocol stack.
DDoS attacks often target many low-security, unprotected, and unsecured protocols. DDoS attacks commonly target Internet communications standards. This is because many of these systems are used worldwide, and it is difficult to modify them quickly. Furthermore, because many protocols have inherent intricacy even after they are re-examined to address current bugs, new vulnerabilities emerge that allow for new types of protocol assaults as well as network assaults.
Examples of protocol DDoS attacks
(BGP) hijacking
Cloud-based services contain a lot of valuable information that data thieves want. This is because they can get helpful information from these services. If there is a data breach from one of these providers, it could be very dangerous. Someone can launch a DDoS attack against a company using protocols higher than the cloud. BGP (Border Gateway Protocol) communicates information about network address spaces.
BGP updates are used to share information between networks. If someone sends a fake update, traffic can go to a different network. This can use up resources and make things congested. Upgrading to a more secure version of BGP would be time-consuming and costly because tens of thousands of network operators worldwide use it.
SYN flood
A TCP SYN Flood is like a supply worker receiving orders from the front of the store.
The driver gets the package, waits for verification, and then carries it in front after receiving a request. The employee gets numerous delivery requests without confirmation until they are unable to carry any more shipments. This can cause them to become overwhelmed.
In this attack, an attacker sends many packets to a victim. The packets have fake addresses. They exploit the handshake that two computers use to start a network connection.
An intruder’s goal is to allow as many connection attempts as possible before shutting down its resources.
Volumetric attacks
This attack aims to use all the internet bandwidth between the target and the rest of the world. The data are sent to a target in one of two ways: amplification or another method for generating tremendous traffic, such as requests from a botnet.
Examples of volumetric attacks
DNS Amplification
The attacker sends small queries to a DNS server, but the server amplifies the query into a much larger payload that crashes the victim’s servers. This type of attack is known as an amplification DDoS assault.
DNS Amplification is a type of network assault in which the attacker sends messages to a victim’s network using DNS servers. The packets may be amplified, making them more difficult to block.
DNS amplification is an attack where someone tricks a DNS resolver into sending them a lot of information. This happens when they send a fake request to the DNS resolver with an address that is not real. Because so many people do this and there are so many DNS resolvers, the victim’s network can quickly be overwhelmed.
Mitigating a DDoS attack
When a DDoS attack hits people, they are often confused. Many security systems do not give detailed information about the traffic coming in. The only thing that is certain about a DDoS is that your clients’ online applications have been inaccessible because of a network outage. The issue worsens if an on-premises security device protects the targeted network.
Using old software is not safe if you have a computer using old software. This is because there may be security risks of which you are not aware. You need to update your computer regularly with the latest patches and software to fix this. However, this can be difficult because new vulnerabilities are constantly discovered. Hackers can use these vulnerabilities to hack your computer and steal your information.
Some attackers may use a DDoS to achieve their goals. However, there are several obstacles. Security solutions that are on-premises cannot prevent an attack from happening. Before the attack reaches an on-premises filtering appliance, volumetric assaults might clog the incoming internet pipe and cause the upstream ISP to be overwhelmed and blackholing all incoming traffic, cutting off the target network from the Internet.
How to defend against DDoS attacks
There are many ways to defend against DDoS attacks. The most important thing is to have a plan in place before you are attacked.
Increase bandwidth
Making sure that your hosting infrastructure can handle a lot of traffic is one of the most important things you can do to protect yourself from DDoS attacks. This means you should plan for unexpected traffic spikes, which can happen when someone hacks into your website. However, increasing your bandwidth does not always mean that you will be protected from DDoS attacks.
When you increase your bandwidth, it becomes harder for attackers to break into your website. However, you can improve your website’s security by using a variety of measures.
Set server-level DDoS mitigation
Some web hosts have DDoS mitigation software on the server level. This function is not always available, so you should ask your web host if they offer it. If they do, find out if it’s a complimentary service or if there is a charge for it. The availability of this service depends on the provider and hosting plan.
Move to cloud-based hosting
Cloud-based hosting is a type of web hosting that uses cloud computing to provide its services. Cloud-based hosting is more scalable and can be more reliable than traditional web hosting.
One of the benefits of cloud-based hosting is that it can be more resistant to DDoS attacks. This is because cloud providers have the resources to absorb and deflect DDoS attacks.
Rate limiting
Limiting the number of requests a server will accept in a certain amount of time can help prevent denial-of-service attacks. Rate limiting can help to stop web scrapers from stealing information and reduce brute force logins, but it might not be enough to handle an advanced DDoS attack on its own.
Use a content delivery network (CDN)
A CDN is a network of servers that deliver content to users based on their geographic location. CDNs can be used to improve the performance of websites and protect them from DDoS attacks.
When you use a CDN, your website’s static content is cached on the CDN’s servers. This content is then delivered to users from the server closest to their location. A CDN can help improve your website’s performance and protect it from DDoS attacks.
You can use multiple CDNs to deliver your website’s static content from different servers worldwide. This makes your website more reliable and powerful. Additionally, using a Multi-CDN solution, you can take advantage of a network of PoPs provided by several CDN vendors.
Blackhole routing
A blackhole route is a great way for network administrators to deal with nearly any problem. When blackhole filtering is done without complex rules, a null route is utilized to reject both good and bad network traffic.
If a DDoS attack targets a server, the Internet service provider (ISP) may try to stop the attack by redirecting all of the site’s traffic to a black hole. This is not ideal because it gives the attacker what they want: making the network inaccessible.
Use a web application firewall (WAF)
A WAF is a type of security software that helps protect websites from attacks. WAFs inspect incoming traffic and block or redirect requests containing malicious code.
You can use a WAF to protect your website from DDoS attacks. However, you need to make sure that the WAF is properly configured. Otherwise, it may block legitimate traffic.
Monitor your network for unusual activity
You should monitor your network for unusual activity. This includes monitoring for sudden increases in traffic and strange requests.
If you notice any unusual activity, you should investigate it immediately. It may be a sign that your website is under attack.
In a nutshell
DDoS attacks can be devastating to businesses. They can cause downtime, lost revenue, and damage to your reputation.
However, you can protect your website from DDoS attacks by using a variety of measures, including server-level DDoS mitigation, cloud-based hosting, rate limiting, and using a CDN. You should also monitor your network for unusual activity and investigate any suspicious activity immediately.
By taking these steps, you can help to ensure that your website is available and accessible to your users, even in the face of a DDoS attack.
DDoS Attack FAQs
DDoS attacks can be complex and require a certain level of technical expertise. However, DDoS-for-hire services now make it easy for anyone to launch an attack.
A DDoS attack aims to make a website or network unavailable. The attacker does this by overwhelming the target with traffic or requests.
DDoS attacks can last for hours or even days. The duration of the attack depends on the attacker’s goals and the available resources.
DDoS attacks cannot steal information. However, DDoS attacks can be used to distract the attention of IT staff while another type of attack, such as a data breach, is carried out.
A VPN can help to protect your devices from DDoS attacks by hiding your IP addresses so the attackers can’t locate your network. However, it will not stop the attack entirely.

security
admin is a senior staff writer for Government Technology. She previously wrote for PYMNTS and The Bay State Banner, and holds a B.A. in creative writing from Carnegie Mellon. She’s based outside Boston.